Workiva and CFGI to Collaborate in the SOX and GRC Space
“Connected reporting capabilities, control testing, real-time collaboration, cloud-based access, stringent security measure and permissions controls” are considered the leading factors behind CFGI offering Workiva to its clients.
In a move to provide its SOX and GRC clients with a tool that will modernize their compliance reporting and management, CFGI, a US-based high-end technical accounts, risk management, and finance advisory services organization, has entered into a partnership with Workiva.
Beyond the ability to access and collaborate with CFGI remotely, users will also benefit from the customizations that CFGI has integrated into the product that facilitate the process and guide the client to accurately complete reporting.
Our Take
In the high-end financial risk advisory and compliance space, specialization in the GRC market is required to support the specific needs of clients who face not only Sarbanes-Oxley rules but dozens of global financial and banking regulations. As compliance requirements continue to drive enhanced reporting and controls, market segmentation will likely continue.
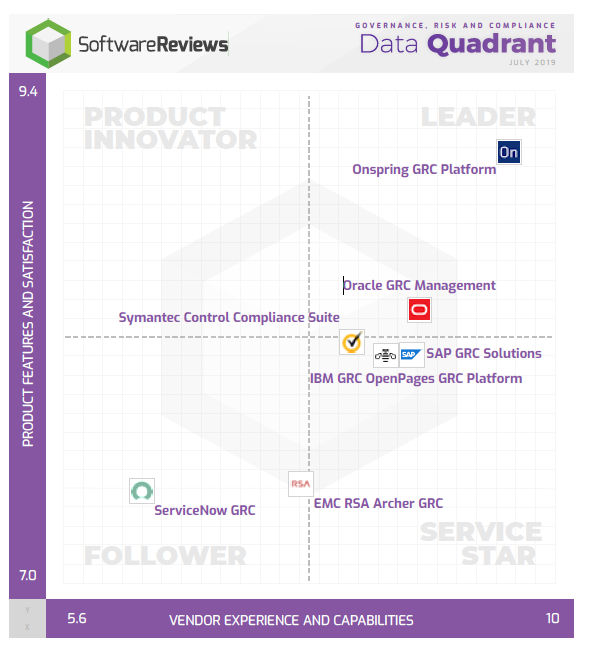
Source: SoftwareReviews GRC Data Quadrant, Accessed May 13, 2020.
Governance, risk, and compliance (GRC) vendors will need to distinguish themselves in the market. New methods of providing value, either through the introduction of machine learning and AI capabilities that assess and evaluate incoming data streams (vulnerability input, compliance, etc.) or through vendor collaboration with value-add services such as CFGI and Workiva, set products apart from the pack. This form of collaboration is another way to improve market penetration.
In recent years, another source of differentiation has been the coupling of GRC with enterprise solutions. An example of this in the financial space is SAP. Oracle has also integrated GRC with its enterprise solutions and in the information service management systems (ISMS) space, and ServiceNow has included its GRC as part of its offering.
GRC is not the sexy toy in the IT software basket, and therefore it must find new ways of adding value and reaching new markets in order to expand market share.
Want to Know More?
SoftwareReviews Governance, Risk and Compliance Category
Build a Business-Driven IT Risk Management Program
Revive Your Risk Management Program With a Regular Health Check