

Security Orchestration, Automation, and Response (SOAR) Tools
What is Security Orchestration, Automation, and Response Tools?
SOAR refers to a solution that allows businesses to collect and analyze data from multiple sources in order to identify security incidents within their IT systems. In addition, SOAR helps to automate the management of security/operational issues, manage security tools through a single interface and coordinate responses to security incidents.
Common Features
- Dashboards
- Integration Capabilities
- Management and Sharing of Intelligence
- Collective Analytics Layer
- Feedback Loop
- Playbooks/Runbooks and Workflow Builder
- Team Collaboration
- Document & Artifact Storage
- Automated Phishing Handling
- Data Model
- Integration with IR Management
- Capable of Use Case Development
- Case Management
- Orchestrate & Automate
Our Methodology
Composite Score
Vendors are ranked by the composite score, which is comprised of feature, capability, relationship, and overall satisfaction scores while factoring in the volume and recency of reviews.
CX Score
The CX score is comprised of the emotional footprint metrics, balanced by metrics related to the overall value of the software, while factoring in the volume and recency of reviews.
Data Quadrant
SoftwareReviews collects user insights that help organizations more effectively choose software that meets their needs, measure business value, and improve selection.
Rankings, results, and positioning on SoftwareReviews reports are based entirely on end-user feedback solicited from a proprietary online survey engine.
Leaders
Products that resonate strongest in the market, balancing features with a great user experience.
Product Innovators
Products that emphasize product features, gaining strong recommendations from their customers.
Service Stars
Products that emphasize a good user experience and build strong relationships with customers.
Challengers
Products that are strong performers in some areas and trail in others. Often up-and-coming vendors.

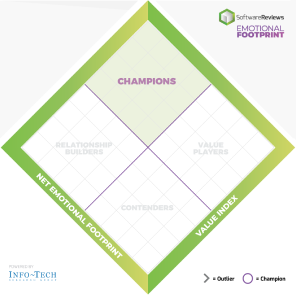
Emotional Footprint
SoftwareReviews collects user insights that help organizations more effectively choose software that meets their needs, measure business value, and improve selection.
Rankings, results, and positioning on SoftwareReviews reports are based entirely on end-user feedback solicited by a proprietary online survey engine.
Champions
Products that resonate highly with users at an emotional level. Users have specific emotional views towards these products like love, trust, and effectiveness.
Relationship Builders
Products that are bulletproof and focus on fulfilling core needs with steady support, not the latest feature.
Value Players
Products that succeed on cost and service effectiveness with users.
Contenders
Products seen as good in some areas and trailing in others. Users look to these for innovation at the edge but aren't fully committed.
Top Security Orchestration, Automation, and Response (SOAR) Tools
2026 Data Quadrant Awards
2025 Emotional Footprint Awards


At SoftwareReviews, we take pride in recognizing excellence. Each year, we present the Data Quadrant Awards to top-performing software products based solely on authentic user reviews, without any paid placements or analyst opinions. These awards highlight software products that excel in terms of features, vendor capabilities, and customer relationships, earning them the highest overall rankings.
At SoftwareReviews, we take pride in recognizing excellence. Each year, we present the Emotional Footprint Awards to top-performing software products based solely on authentic user reviews, without any paid placements or analyst opinions. These awards shine a spotlight on software vendors who excel in crafting and nurturing strong customer relationships.


Get Instant Access<br>to this Report
Get Instant Access
to this Report
Unlock your first report with just a business email. Register to access our entire library.
© 2026 SoftwareReviews.com. All rights reserved.








